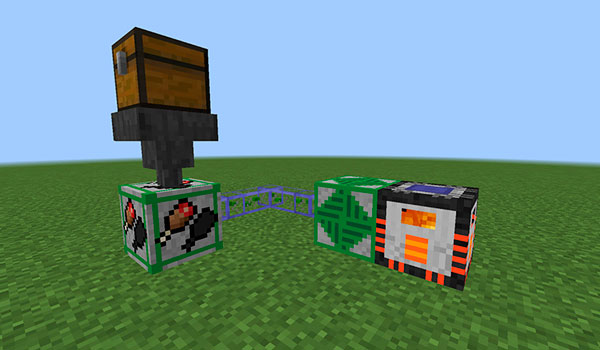
Advanced Inventory Management es un mod que nos ofrece diversos objetos que nos aportarán funcionalidades para automatizar ciertos procesos dentro del inventario de nuestro personaje. Incluso podremos olvidarnos de algunas acciones rutinarias que todo jugador debe realizar en el inventario.
Conectando máquinas y dispositivos, junto a redes de bloques estáticos, dichos sistemas podrán acceder y manipular el contenido del inventario de nuestro personaje sin que nosotros intervengamos en el proceso.
Las funcionalidades que nos aportan estos sistemas, por ahora, son tres. Dichos sistemas serán capaces de guardar la experiencia acumulada, alimentar y curar al personaje de forma autónoma. Es decir, sin que tengamos que hacerlo nosotros.
| Versión Minecraft | Links |
|---|---|
| 1.12.2 | Descargar |





ENLACE ROTO
jaja
estavueno
sfsffddffdgdgd gdgd/ gdh dgddgfdgdfgdg dg /gd gdgdg d/g dgdf/dd fgdhfgdf /fdgdfsfasfs s sf s/ ds sf df/ gfd gd/ g/fg/fc/g fh/ d/g/fdf/ gzd/hfgsd<fdg/f s/e fdf/ s fs /fsd f/ s