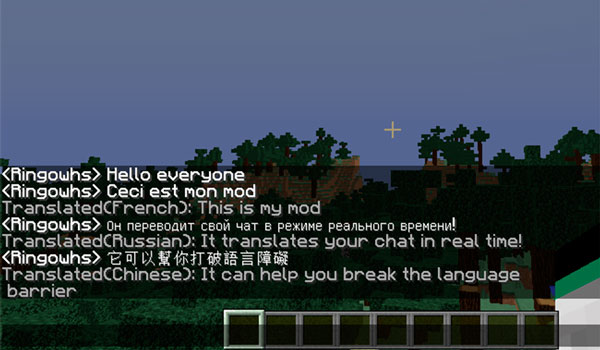
Real Time Chat Translation nos ofrece un traductor en tiempo real de todo aquello que se publica en el chat de Minecraft, lo que se convierte en una utilidad interesante para todos aquellos jugadores que juegan en servidores donde se hablan otros idiomas, pues podrá saber que es lo que dicen los jugadores de servidor sin saber el idioma en cuestión.
Para realizar la traducción en tiempo real, este mod utiliza la API del buscador ruso Yandex, que ofrece gran cantidad de traducciones, entre ellos por supuesto el Español. Aunque como ya sabrás, los traductores no son muy fiables a la hora de interpretar frases, pero siempre nos permitirán entender algo más que si no tenemos el traductor.
El mod nos permite configurar diversas opciones sobre su funcionamiento, accediendo al menú de personalización y configuración, al cual se accede al pulsar la tecla "Y". De todos modos es recomendable echar un vistazo a este vídeo para ver cómo es su funcionamiento.
| Versión Minecraft | Links |
|---|---|
| 1.12 – 1.12.2 | Descargar |




